Red-Black Concept, Why Separation Matters
Those working in computer technology and digital communications may come across the Red-Black Concept, though it is not commonly used. The Red-Black Concept can be traced back to early efforts in Communications Security (COMSEC). Digital communications are often encrypted to protect the data being sent over networks. The https you see in the address bar of a web browser, often alongside a padlock icon, is an indicator of encrypted communications. The Red-Black Concept is concerned with how the parts of computer and communications systems, and the facilities that hold them, deal with data before and after it is encrypted. This is to help handle classified and unclassified data correctly and maintain good data security.

An old U.S. Navy light (ID-866/SG) to indicate classified communications routing.
Keeping Data Secure is Important
Humans have always been concerned with keeping secrets, particularly in times of war. Armed forces commanders do not want the enemy to know the orders given to the fighting personnel. To keep information secret encryption can be used. The Roman general and dictator Julius Caesar used the Caesar cipher, his secret code, to protect his military communications. In World War II the Prime Minister of Britain Winston Churchill would communicate with US President Franklin D. Roosevelt in the White House in America over a line scrambled by a machine called SIGSALY. The Transatlantic Telephone Room was a tiny room disguised as a private toilet located within the British Government's War Rooms in London. A telephone in the room connected to the SIGSALY machine. Here is a description from that link:
"A scrambler codenamed Sigsaly was connected to this room which created the hot-line enabling Churchill and the President of the United States to have vital discussions with total security. This old basement broom cupboard was converted in 1943.
The London terminal of the telephone scrambler, codenamed X-Ray, was so large it had to be located in the basement of Selfridges department store in Oxford Street.
Conversations were transmitted by cable from the hot-line to the Selfridges site where they were enciphered and sent by cable to Scotland and from there by radio waves to the President in Washington."
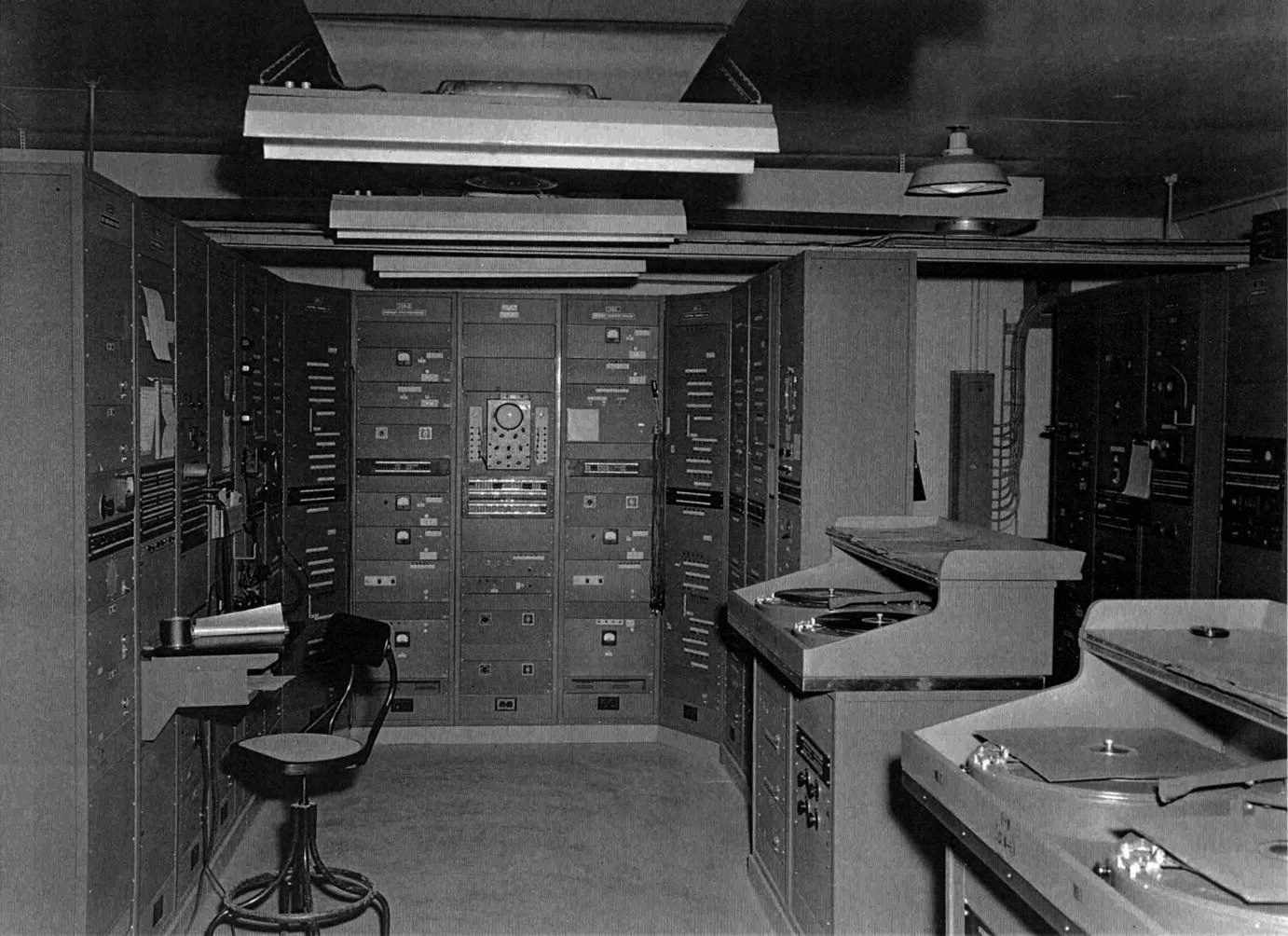
Achieving the first practical digitisation and encipherment (scrambling) of speech before the age of transistors and computers was a major achievement. However, the machines used were very big and consumed a lot of power. Here is a picture of SIGSALY (from the US National Archives):
The military has long used systems to secure data, but data security is important for everyone. The world is run by digital systems. We communicate and spend money via our smartphones and laptops, making our personal data, and all data important. This is why it is encrypted and why data protection laws exist in many countries.
Leaking Secrets
There is a problem with using electronic systems for communication, they leak information. When electricity travels through a wire it generates an electromagnetic signal. It is the reason we are able to listen to music on the radio. Radio signals are purposely generated and used to listen to our favourite radio station. However, all electronic equipment makes some form of radio wave signal. If the enemy can pick up the signals from the equipment, then they may be able to work out the messages being transmitted, and that goes for a scrambling machine that is trying to keep messages secret. Solutions were needed once the military discovered that any wire could potentially leak secret information to a sensitive enough receiver.
A 1973 National Security Agency (NSA) report was titled A History of U.S. Communications Security. It covers the background of what is known as TEMPEST. This is a codename for work on reducing unwanted electromagnetic signals from systems, particularly military communication systems. In World War II the teleprinter or teletype (TTY) was commonly used for communications. The Bell Telephone company provided the U.S. military with the 131-B2 mixer. It took a tape used as the secret for encrypting communication, mixing it with the text to be kept secret. This encryption machine was known as SIGTOT. The Bell Telephone engineers discovered that spikes would appear on an oscilloscope in their lab when the mixing machine was operating. They then used those spikes to work out the text, called plaintext, that was being encrypted into the ciphertext. When they proved this capability to the U.S. military it was the start of a new industry, an industry concerned with the prevention of information leakage from indirect sources. Hacking for secret information indirectly is now commonly known as side-channel attacks. The military and their contractors now use TEMPEST specifications for the installation and testing of equipment. This provides them with the technical requirements to help prevent inadvertent information leakage.
Red/Black Concept Definition
TEMPEST requirements become increasingly sophisticated and expensive and several different methods are employed. These methods include equipment shielding, filtering and masking of signals, and keeping a clear and wide physical space around equipment. To help with TEMPEST engineering the layout of electric and electronic circuits became important. The engineers needed to separate the circuits carrying the classified plaintext from those carrying the less important communications. This isolation became known as red/black separation. The classified plaintext travels only on designated red circuits and the unimportant data travels only on designated black circuits. This is the Red/Black Concept in COMSEC. From FED-STD-1037C (Telecommunications: Glossary of Telecommunication Terms):
RED/BLACK concept: [The] separation of electrical and electronic circuits, components, equipment, and systems that handle classified plain text (RED) information, in electrical signal form, from those which handle unclassified (BLACK) information in the same form.
It makes sense to use the colour red for unencrypted data. Red is often used to signal danger and important data that hasn't been secured could be dangerous if it got leaked. Hence areas and equipment classed as red could be given additional physical and procedural security attention. Military specifications, for example, MIL-HDBK-232A (Red/Black Engineering-Installation Guidelines), contain instructions on physical building and equipment requirements and wiring configurations to maintain red/black separation.
Other Red/Black Uses
With data encryption being very common, the red/black concept in security is no longer often seen. This is disappointing as it provides a good reminder of the need to be aware of the locations in a system when data is not encrypted. At those points the system is weak and care should be taken. After all, data security is only as good as its weakest point.
However, you may come across the use of red/black in other areas, for example in the deployment of new versions of software onto running servers. When a new version of live server software is deployed it becomes the black version and begins to accept the server connections. Once the older red version no longer has any connections it can be removed from the server. This achieves the software upgrade without taking the server down.
Then there is the red/black tree used in computer science to aid fast data searching. Therefore, when someone is talking to you about the red/black concept, make sure you both know which red/black concept is being used.
Confusingly, blackers are devices used to encrypt communications. It could be considered that once data is encrypted it has effectively been blacked out. Indeed, in the late 1970s the NSA funded a Blacker program for encryption and follow-on programs to build devices called Blackers for encrypted communications, see this email on some background.
Summarising the Red/Black Concept
The red/black concept divides a security system into the areas covering the classified information or plaintext from those handling less important data. The classified plaintext areas need extra care until the data becomes encrypted into ciphertext. Therefore, the red designated areas signify the extra care required. This red/black separation classification helps with the system, procedural, circuit, and software designs for achieving security aims.
See Also
- For a list of all the articles in Tek Eye see the full site Index
Author:Daniel S. Fowler Published:







